Tech Terms
Sideload — The standard way to install an app on an iOS or Android device is to download it from Apple's App Store or Google's Play Store. Sideloading an app bypasses the app store, installing the app directly from a local device.
***Heads Up***
Yesterday, I responded to this essay in the New York Times. You can read it by clicking the “card” below.
Restraint advocates, and particularly those on the “new right,” speak eloquently of a United States awash in freedom and resources, but never explain how they intend to rid us of the inescapable foreign commitments and actions necessary to secure this domestic prosperity and tranquility.
News Corp. Hit by Cyberattack
What’s New: The American media and publishing company, News Corp., disclosed that it has been breached by suspected China-based hackers, according to the Wall Street Journal.
Why This Matters: News Corp. is massive and its assets include Dow Jones & Company (publisher of the Wall Street Journal), News UK (publisher of The Sun and The Times), News Corp Australia, REA Group, Realtor.com, and HarperCollins.
Key Points:
The breach was discovered on January 20th, but is now suspected to go back at least until February 2020.
News Corp. says it immediately notified law enforcement and then hired the Mandiant Inc. cybersecurity firm.
“Mandiant assesses that those behind this activity have a China nexus, and we believe they are likely involved in espionage activities to collect intelligence to benefit China’s interests,” said David Wong, vice president of incident response at Mandiant.
A spokesman for the Chinese Embassy, Liu Pengyu, said, “We hope that there can be a professional, responsible and evidence-based approach to identifying cyber-related incidents, rather than making allegations based on speculations.”
While the scope of the breach is still being determined, The Wall Street Journal quotes people briefed on the matter as confirming that the attackers gained access to reporters’ draft articles, emails, and other data.
What I’m Thinking:
Two years is a very long time. In cybersecurity, the time between when a breach occurs and when it is discovered is called the Breach Detection Gap (BDG) or dwell time. Over the last several years the average BDG has dropped significantly, with a current average of 146 days, according to FireEye, while the average cost of a data breach has risen to a 17-year-high of $4.2million. The fact that this breach extends to more than 700 days means we’re looking at an attack with very large implications — most of which aren’t even known yet. Also, once a sophisticated attacker gains access to a victim’s network, they move “laterally” through that network while also “escalating” their “privileges” (i.e., expanding their access to the network, often by stealing the credentials of users with broad permissions). Counterintuitively, as an attacker expands their presence on a network — if they’re careful — they can hide their activity better by understanding and avoiding security measures and by masking their activities to look more like normal network traffic. This is why, according to Trustwave, 81% of “reported intrusions are not detected by internal security processes but rather by news reports, law enforcement notifications, or external fraud monitoring.”
News Corp. is a sweet target. One of the best ways to maximize limited intelligence gathering resources is to choose targets with the most “bang for the buck” — and boy, this media conglomerate offers a lot of bang. Think about it: by popping News Corp. you get access, not only to all of their published materials, but also all of their unpublished research on virtually every news-worthy topic you can imagine. You get reporters’ notes, sources, ideas, etc. You get their private communications from around the world as they report on world leaders, business tycoons, human rights advocates, and the foreign press. The attackers even get a detailed understanding of how a story is generated, reported, and published — giving them even more insight into how they can shape and manipulate this process for their own purposes. Now put this capability in the hands of the Chinese government’s hacking enterprise, an enterprise the FBI Director says is “bigger than those of every other major nation combined,” and you’ve got yourself a real problem.
I’m concerned about a looming cyber shrug. This is just one of the many, many cybersecurity incidents that are reported every day. Even for me, the unrelenting drumbeat of just the truly huge data breaches threatens to recede into the background as a low-level “hum,” because no one can keep up with them all and no one should have to be on high alert all of the time. But, just because these attacks are familiar doesn’t mean they are no big deal. Our national cybersecurity has been a hot topic for policymakers for the last several months but I’m concerned that, in the face of what feels like an overwhelming challenge and no clear way forward strategically, political will and attention will ebb away. And then one day, our enemies will finally leverage the data, influence, and compromises they have amassed and we’ll have nothing left to do but pick up the pieces. This is why Congress needs a select committee on cybersecurity — to keep policymakers’ eyes on the ball and to drive executive accountability. The threat couldn’t be any more clear and we shouldn’t shrug it off.
Pentagon Suppliers Struggling to Meet Cybersecurity Requirements
What’s New: Only one in four defense contractors are in compliance with the Department of Defense’s cybersecurity standards, according to the Defense Industrial Base Cybersecurity Assessment Center (DIBCAC).
Why This Matters: The standards were originally designed to protect critical weapons systems from foreign hackers, but the Biden administration is planning to expand them to more than 200K companies across the defense supply chain.
Key Points:
The Cybersecurity Maturity Model Certification (CMMC) was first announced in 2019 and seeks to formalize the cybersecurity assessment and reporting of critical defense contractors.
Before this, most defense industrial base cybersecurity assessments were based on a self-assessment and a report against NIST SP-800-171 standards.
According to the DIBCAC Director Mr. John Ellis, however, three-quarters of the 220 contractors that have been assessed by the Pentagon have failed to meet these baselines and are now operating under “special agreements.”
“It is clear that a very large number of companies have a very great deal of work to do” to meet the CMMC standards, said Robert Metzger, an attorney and former member of the Defense Science Board Task Force on Cyber Supply Chain.
Despite these failures, the White House continues to expand the rollout of these standards to the entire defense industrial base over the next few years.
What I’m Thinking:
The CMMC is a good idea, but it was always going to be painful. Having a set of common, verifiable cybersecurity standards for the folks who build the stuff we need to fight and win wars is obviously important and not too much to ask from defense contractors. That said, suppliers are not wrong when they complain that some of the CMMC’s 110 requirements are unclear, expensive, and can even be unfair. Further, we’re talking about an industrial base of more than 200K companies worth more than $500 billion. This means the government is trying to wrangle and shape a massive challenge and it was never going to be easy.
The best we can do is just keep at it. Implementing the CMMC is going to take time and patience — but it’s worth it. Expanding the CMMC will require even more time and patience — but this too will be worth it. Even if these efforts take decades (and they likely will), the nation will be better off than we were just a few years ago. So everyone needs to settle in, get comfortable, and get after it. Eventually, we’ll need to think about how to turn the screw on companies who aren’t coming into compliance quickly enough. But I suspect now is largely the time for carrots, not sticks.
Skydio’s Win is a Good Sign
What’s New: The Army has chosen U.S. drone maker Skydio for its Short Range Reconnaissance (SRR) Program of Record, according to a company press release.
Why This Matters: The contract has a base year value of $20 million and could be worth nearly $100 million over five years — constituting one of the most significant DoD contracts with an agile, non-traditional defense contractor out of Silicon Valley.
Key Points:
The Army teamed up with the Defense Innovation Unit to review more than 30 unmanned reconnaissance and surveillance proposals.
Skydio’s X2D was selected based on “soldier feedback and design review packages intended to assess the overall product performance, quality, and production readiness.”
“With the SRR program, our soldiers will now have access to the most advanced capabilities in the world in this class," said Skydio CEO, Adam Bry. "Skydio drones deliver unparalleled situational awareness and ease of use in the most demanding situations thanks to Skydio Autonomy.”
Here’s a quick video of a Skydio drone in action:
What I’m Thinking:
Full disclosure: I know and like these folks. I’ve had the opportunity to spend time with Adam and his team and they are really impressive.
Their kit really works. There are lots of drone companies out there but Skydio is known for its autonomous AI, which allows their platforms to avoid objects, fly routes, map objects, and complete other tasks with minimal effort from a human pilot. They won this contract for a reason.
I’m encouraged by what this could mean. I’ve long said that one of the key challenges to incorporating non-traditional defense contractors into Pentagon acquisitions is the infrequency with which DoD awards these companies with real programs of record. Typically, “start-ups” like Skydio will only get proof-of-concept or other limited funding that also comes with a lot strings that can make doing business with the military difficult or even impossible. Over the last several years, the government has evolved its authorities and processes to be more agile and, I hope, we’ll be seeing more of these contracts very soon.
Let’s Get Visual: Using Planets to Visualize the Speed of Light
From The Visual Capitalist:
We often come across the term “light-year” in the context of space travel. But what does it actually mean?
A light-year is the distance light travels in one year. At a speed of 186,000 miles/sec (300,000km/sec), light travels 5.88 trillion miles (9.46 trillion km) in a year—a distance well beyond immediate comprehension.
Scientists created the term light-year to measure astronomical distances beyond the confines of the Earth. And in the vastness of space, light photons, which can go around the Earth 7.5 times in just one second, seem slow.
The above animation from planetary scientist Dr.James O’Donoghue helps put the speed of light into a broader perspective while highlighting the vast distances between celestial bodies.
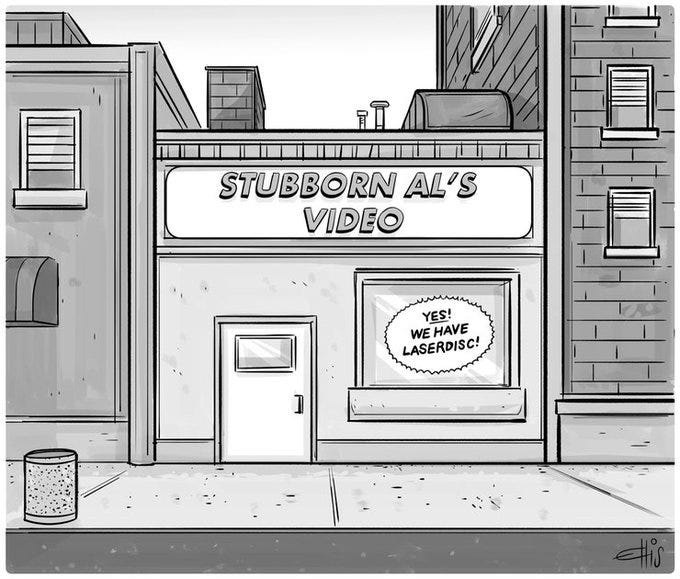
Nerd Humor
Quick Clicks
That’s it for this Friday Brief. Thanks for reading, and if you think someone else would like this newsletter, please share it with your friends and followers. Have a great weekend!